Wednesday, November 30, 2011
Turning in Laptop at End of Employment without Claiming Privilege as to Contents Effects Waiver
http://ow.ly/7Ky2U
An article on the Gregory P. Joseph website.
The article discusses the case Aventa Learning, Inc. v. K12, Inc., 2011 U.S. Dist. LEXIS 129928 (W.D. Wash. Nov. 8, 2011).
The case involves two separate employees claims of attorney-client privilege after they turned in their corporate laptops upon the end of their employment.
In the first instance, the employee never claimed attorney-client privilege upon turning in his laptop. This was deemed to be a waiver of any claim of such privilege.
The second employee did claim privilege of the files on the laptop. However, with respect to the emails, the Court held there was no reasonable expectation of privacy, thus no privilege extended to the emails. The second employee was held to have known of the email policy of the corporation, since he held a management position. Based on the employee handbook policy, the Court stated the employee could not have had a reasonable expectation of privacy in his email communications.
Legal Responsibilities to Preserve Data–E-Discovery Best Practices
http://ow.ly/7KxpX
An article by Laura Waldman on the Frank nextpoint blog.
This article discusses best practices for preserving data that may need to be required for an eDiscovery process.
The article states, "These 14 guidelines place emphasis on the importance of evolving technology and the responsibility to preserve data. Although the guidelines are intended to provide New York practitioners with “practical, concise advice in managing electronic discovery,” all legal professionals can benefit greatly from thoughtfully reviewing and adjusting their practice accordingly." Al link to the 14 referenced guidelines is provided in the article.
eDiscovery Case Law: Produced ESI Doesn’t Need to be Categorized, Even When Voluminous
http://ow.ly/7JLkn
An article by Doug Austin on the eDiscovery Daily Blog.
This article focuses on a criminal case in which the defendants sought an order for the government to categorize produced electronically stored information into four groups.
The article states, "In United States v. Rubin/Chambers, Dunhill Ins. Servs., No. 09 Cr. 1058, 2011 WL 5448066 (S.D.N.Y. Nov. 4, 2011), the defendants sought to compel re-production by the Government of ESI in categorized batches relating to transactions with certain characteristics. Judge Victor Marrero of the Southern District of New York denied the defendants’ motion." A link to the case opinion is provided in the article.
The article goes on to describe the fact that in this case the data produced by the government was fully searchable, hence further categorization was not held to be required. The article additionally states, "According to the court, there were several differences between this case and United States v. Salyer, Cr. No. S-10-0061 LKK (GGH), 2010 WL 3036444 (E.D. Cal. Aug. 2, 2010) – where the defendant’s motion for the identification of Brady material was granted. Those included that:
- The already disclosed materials were searchable;
- Defendants had access to corporate assistance;
- There was ongoing parallel civil litigation and “multiple defendants” with “overlapping discovery needs,”;
- Defendants were not incarcerated; and
- “[T]here [could] be no straight-faced claim of a ‘small defense team.’”
P.S. The holding in this particular case seems limited to criminal matters involving government investigations. Depending on the jurisdiction, civil litigation may involve a wholly different outcome upon request for categorized ESI.
How to Fulfill Document-Preservation Obligations
http://ow.ly/7JJNs
An article by Barbara S. Nicholas published by the Texas Lawyer, and appearing on law.com on the LTN webpage.
This article focuses on the duty of counsel to ensure that evidence potentially relevant to a litigation is being preserved. These preservation obligations extend to not only paper records, but also to all forms of electronically stored information.
The article states, "An attorney should issue a written litigation hold immediately upon notice of a triggering event (e.g., potential claim) or a suit, whichever comes first. In a perfect world, the initial demand for litigation hold would contain the universe of information necessary to capture all systems and parties relevant to the claim or suit.
But the real world is not always perfect. Lawyers and clients rarely have complete information at the outset of a dispute. As such, document preservation is not a one-time process initiated at the commencement of a case or upon some other pre-litigation triggering event. It is an ongoing obligation, continuing throughout the course of the litigation."
The article goes on to provide some advice to attorneys as to how to properly meet their obligations. Four tips are suggested, and narrative discussion is provided in the article around the following four topics;
- Communicate;
- Identify;
- Update;
- Produce.
The article further states, "If the documents are not reasonably available in the ordinary course of business, a lawyer should object, as the Weekley court noted, "on grounds that the information cannot through reasonable efforts be retrieved or produced in the form requested.""
Skype in eDiscovery
http://ow.ly/7JIXA
An article by Stuart Clarke on the articles.forensicfocus.com website.
This article discusses forensic collection of data from the Skype video chat, and messaging, internet service. The article projects that audio electronically stored information will become a more important focus in eDiscovery in the near future, and such collection techniques require specialized strategies.
The article states, "Skype claim that during peak times they have around 20million users online (http://about.skype.com/). This figure is hardly surprising when you consider that Skype runs on a range of popular electronic devices including computers and smart phones. Current versions of Skype support instant messaging (IM), file transfers, SMS, standard speech calls and video calls. Helpfully, Skype records our activities in a non-encrypted form on the local device. Furthermore, the average user rarely disables the logging functionality of Skype. Consequently, all IM conversations, call records and details of file transfers are stored locally, be it a computer hard drive or a mobile device. This might not come as a surprise to many of you, and I expect that most Skype users have at some point noticed you can view your Skype message history at the click of a button."
The article further explains, "Skype records history in various database tables containing countless fields of data, which in honesty is not user friendly and requires the analyst to have some database knowledge. Many of the fields within the database are not of any great interest for an electronic discovery matter. Yet perhaps the real reason this data is ignored is the format of the Skype database file, which is a SQLite database. There are few computer forensic or eDiscovery solutions available to fully index and present the data from a SQLite database in an understandable manner to a non-technical person." The article goes on to provide advice on how to possibly obtain useful data through specific forensic techniques.
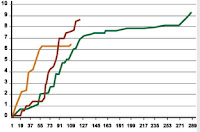
The article also shows how certain collection tools can be used to present graphical representations of communication patterns, particular photos provided through the use of Nuix are provided in the article, and one is presented here below:
Tuesday, November 29, 2011
Navigating eDiscovery in the Cloud Shouldn't Be That Difficult
http://ow.ly/7Jdp2
An article by Charles Skamser posted on the blog eDiscovery Paradigm Shift.
The article discusses eDiscovery and cloud computing and references prior articles on this topic. In addition, the article states that there is confusion about what eDiscovery in the cloud truly is. The article provides info as to what is NOT ediscovery in the cloud, and goes on to describe what is a true eDiscovery in the cloud workflow.
The article states, "eDiscovery in the cloud ultimately means having a virutal eDiscovery process that actually runs in the cloud right alongside of your cloud storage and allows you to perform, Early Case Assessment (ECA) including First Pass Review, possibly preservation and legal hold management, definitely forensically sound collection and the generation of an industry standard load file and/or full on document review and production. In addition, eDiscovery in the cloud also means that you can operate these processes remotely through an Internet based user interface and don't have to have operational bodies physically inside the cloud data center(s) to perform any of the normal magic that is currently required by many of the legacy hosted eDiscovery platforms."
Obama wants feds to digitize all records
http://ow.ly/7J2vd
This article written by Lucas Mearian and appearing on the computerworld.com website.
This article discusses the fact that Federal Agencies have been given a 4 month window in which they have been requested to provide proposed solutions as to how they can digitize all of their records, and add them to the National Archives and Records Administration (NARA), where feasible.
The article states, "Paul Wester, chief records officer for the U.S. Government, said in an interview with Computerworld that the president's directive is really about driving a more open government where citizens can access information in a more "Web 2.0" format.
"No one is completely electronic now, and that's one of the challenges we're driving toward with the presidential directive," Wester said. "The wider direction is about open government and transparency, being more responsive to citizens, implementing more open business operations" between agencies who can then interact with one another.
Wester said new laws and regulations may be needed to move the process of creating a more unified electronic records system forward."
According to the article NARA recently scrapped a 10 year effort to attempt to create an electronic records archive, due primarily to cost overruns.
Going Dutch on eDiscovery: Hosted Review Agreement Trumps Prevailing Party Cost-Shifting
http://ow.ly/7J0KF
An article by Joshua Gilliland, Esq. posted on his blog, Bow Tie Law.
This article discusses the concept of cost sharing for an eDiscovery review platform, as well as the possibility that cost-shifting will be sought at the conclusion of a case.
The article states, "In a patent dispute, the parties agreed to use a online review platform for the production of email and to share the costs. The prevailing party in the lawsuit won on having their hosting costs of $234,702.43 shifted to the opposing party. The losing party appealed and the Court of Appeals reversed the cost-shifting award.Synopsys, Inc. v. Ricoh Co. (In re Ricoh Co.),2011 U.S. App. LEXIS 23495, 9-12 (Fed. Cir. Nov. 23, 2011)."
The review platform was used for production, and taxes were held to be applicable to the database. In addition, the Court found that the costs should not be awarded, since there was a prevailing cost sharing agreement in place between the parties for the hosting costs.
The article states, "It is good that courts recognize hosting fees for an online review platform as recoverable costs. This opinion puts parties and service providers on notice to watch out for the terms in a shared hosting agreement. If there is a possibility a party may seek costs for a shared hosted review database, a clause should be put into the agreement about cost-shifting for a prevailing party. This should be a Rule 26(f) meet and confer topic if a shared-hosting platform is being considered."
BEST LEGAL DEPARTMENT OF THE YEAR
http://ow.ly/7IP7Q
A post on the corporate counsel webpage of the website law.com
This article provides insight into the 6th annual awards provided for Best Legal Department, and provides articles and information regarding the nominees, and the chosen winner. Videos are provided by links in the article.
Congrats to this year's winner, Google.
Facebook: a cunning litigator's best friend
http://ow.ly/7IKSU
An article by Michael Legg posted on the Sydney Morning Herald website.
This article discusses the use of Facebook as a means of finding evidence relevant to a litigation.
The article states,"In the US and Canada over the past few years judges have been willing to compel the disclosure of material on social media to the other side in litigation."
The article further states, "...privacy settings do not prevent a court permitting discovery or issuing a subpoena to retrieve information on a social media site. Facebook's policy recognises as much when it says, "We may share your information in response to a legal request (like a search warrant, court order or subpoena) if we have a good faith belief that the law requires us to do so".
Material available for litigation may also include content stored on a mobile phone."
Feds Play Movie Industry Messages on Seized Websites — Legality Unclear
http://ow.ly/7IAdH
An article posted by "paid content" on the Mashable.com website.
This article discusses the seizure of 150 websites by Federal Authorities yesterday (Cyber Monday) due to allegations that the sites were selling pirated goods, and/or "knock-offs".
The article states, "Federal law enforcement agents celebrated Cyber Monday in their own peculiar fashion by seizing 150 websites to go with along with the 72 they bagged last year. And now the agencies are using the captured trophies to play videos blasting movie piracy — even though many of the sites had little to do with the film industry and nothing in the law says they can use them this way."
In addition, the article describes a new and creative use of the seized websites, "There is another odd phenomenon that is coinciding with these seizures that typically take place near events like Cyber Monday or the Superbowl. Namely, some of the seized websites are no longer just displaying a U.S. law enforcement badge but are instead redirecting users to YouTube to watch a public service announcement about the effects of DVD piracy on the film industry." A link to the referenced PSA is provided in the article.
The author states that it is unclear if the Federal agencies have the authority to use the websites they have seized in such a way, and that they are apparently relying on drug seizure laws to use this tactic. However, the authority the Federal agents are relying upon does not seem to be a clear fit to allow the use of seized websites in such a manner.
e-Discovery in The Cloud Not As Simple As You Think
http://ow.ly/7Iwys
An article by Barry Murphy published by Forbes on the Forbes.com website.
The article discusses "Cloud" based computing services, and focuses on how they are dealt with when it comes to an eDiscovery process.
The article mentions the City of Los Angeles, and discusses their dissatisfaction with the Cloud model they chose to adopt two years ago. Security of data, and the inability to provide eDiscovery services for the data in the cloud are mentioned as complaints that L.A. has had regarding their attempt to implement a cloud based system.
The article further states, "A large majority of respondents to our “The Cloud and eDiscovery” survey are using cloud-based solutions, ranging from hosted email archiving to popular applications like Salesforce.com and QuickBooks. Companies are knowingly or unknowingly storing discoverable information assets in the cloud. But the real question they should be asking is, “Do we have a plan in place for eDiscovery should the need arise?”" A link to the referenced Cloud survey is provided in the article.
According to the article, "Only 16% of respondents indicate that an eDiscovery plan is in place for cloud-based information management solutions. Granted, only 26% actually responded that they do not have an eDiscovery plan in place, but what is truly scary is the 58% who don’t even know if a plan exists. This means that many organizations, when they face an investigation or litigation, will be left scrambling in a reactive firefight to collect information from the cloud. That will inevitably lead to higher costs and more difficulty making informed legal decisions quickly."
Federal Circuit Takes on Database Cost Taxation
http://ow.ly/7IsMR
An article by Mark Michels on the EDD Update blog.
The article addressed taxable costs and discusses a specific case that held that eDiscovery services associated with a database can be taxable.
The blog post states, "...the Court of Appeals for the Federal Circuit issued an opinion finding the taxation of discovery database costs is permissible under 28 U.S.C. § 1920 and Federal Rule of Civil Procedure 54(d)(1). See In Re RICOH Company, LTD. Patent Litigation, No. 20-11-1199, (Fed. Cir. November 23, 2011)." A link to the case opinion is provided.
The court further stated, "The Federal Circuit, applying Ninth Circuit precedent, held that the costs of producing a document electronically can be recoverable under 28 USC § 1920(4) which provides for recovery of “exemplification” costs. It also found persuasive N.D. Cal local rule 54-3(d)(2) which permits taxing the “cost of reproducing disclosure or formal discovery documents when used for any purpose in the case.”"
Private Clouds Could Be Mushroom Clouds for IT
http://ow.ly/7IqKF
An article by Mary Jander on the internetevolution.com website.
This article discusses private cloud computing, and outlines the challenges associated with such a business model.
The article states, "This point was made by ThinkerNetter Mary Shacklett in a blog last August. Many IT departments may not be ready for private clouds, Mary said, because delivering services on demand to various internal customers requires IT to perform at contracted service levels, as do outside service providers. Private clouds, Mary said, require IT to cast off any semblance of finger-pointing or blame-gaming, either internally or with suppliers. "Silos of technical expertise have to be broken down, so that experts can collaborate and cooperate with each other as they rally behind the successful operations of an individual business service."" A link to the blog post is provided in the article. In addition, other articles on this topic are also referenced, and links are provided to those items.
The author goes on to state, "Even if the term private cloud is applied to things other than offering standardized IT services to enterprise customers at guaranteed service levels, the move is likely to pinch IT. And for some organizations, it could doom the current state of affairs.
Still, most observers note that IT is undergoing unprecedented pressure to produce and perform. So flattening the structure, eliminating silos, and upping the service ante may be changes that help IT to cope with the pressure."
Monday, November 28, 2011
Uncovering hidden budget to manage long-term legacy data liability
http://ow.ly/7HROM
An article by Dennis Kiker and Jim McGann on the insidecounsel.com website.
The article provides insight in ways to find methods to reduce legal costs, even when money in the budget to invest in technology does not seem to exist.
The article states, "One area of escalating risk and cost to the enterprise is unmanaged information. Whether resident on seemingly self-propagating data archives, forgotten shared drives or mounting stores of legacy backup tapes, unmanaged information not only accounts for an increasingly large percentage of a company’s IT budget, it also represents an unknown and seemingly unknowable risk. How can legal teams help their clients proactively manage user data within tight budgets and ensure that corporate information management policies are implemented?
Corporate IT departments consume a large portion of the corporate budget, and they also are the teams that manage all user data. Finding money in these already strict budgets and delivering the tools to enable IT to implement policy can seem like insurmountable challenges. However, by leveraging available technologies, a large component of typical IT budgets can be freed up and used to manage long-term liability."
The article further states, "Using technology that can scan legacy tapes and index the information on them, it is possible to identify data relevant to an existing legal preservation obligation and quickly extract that data into a more suitable archive for long-term storage. The balance of the data, typically 90 percent or more, can be quickly and permanently purged, eliminating a hidden source of potential future liability. The cost for the technology and labor required to remediate a store of backup tapes and manage long-term liability is less than the cost to store the tapes annually. In other words, eliminating the hidden risk resident on legacy backup tapes generally will pay for itself—sometimes in a matter of months."
Thus identifying ways to reduce existing expenses, and create new more efficient ways to store information, and remove what does not need to be stored, can more than pay for itself.
‘Few’ solicitors understand e-disclosure, says Jackson
http://ow.ly/7HG18
An article by Victoria Ramsey appearing on the lawgazette.co.uk Law Society Gazette website.
This article provides warning from Lord Justice Jackson in the U.K. regarding the need for solicitors to understand eDisclosure.
The article quotes Lord Justice Jackson as stating, "‘I hope that solicitors will take seriously the need to have the relevant person present at the first CMC. Fundamental decisions are likely to be made about disclosure. If the person who is responsible for disclosure and understands what material exists does not attend, inappropriate costs orders may be made with drastic costs consequences for the client.’"
‘Few’ solicitors understand e-disclosure, says Jackson
http://ow.ly/7HG18
An article by Victoria Ramsey appearing on the lawgazette.co.uk Law Society Gazette website.
This article provides warning from Lord Justice Jackson in the U.K. regarding the need for solicitors to understand eDisclosure.
The article quotes Lord Justice Jackson as stating, "‘I hope that solicitors will take seriously the need to have the relevant person present at the first CMC. Fundamental decisions are likely to be made about disclosure. If the person who is responsible for disclosure and understands what material exists does not attend, inappropriate costs orders may be made with drastic costs consequences for the client.’"
Feds seize 150 websites in counterfeit crackdown
http://ow.ly/7HF2V
An AP article by Alicia Caldwell appearing on yahoo.com
This article states that U.S. Officials have taken down 150 websites today in a Cyber Monday crackdown, aimed at protecting consumers from sites that are selling "knock-off" merchandise.
The article states, "The government seized the domain names for the sites that sold everything from fake replica NBA jerseys to replica Louis Vuittonhandbags and imitation Ugg boots."
Local authorities report more than 1000 personal data breaches in last three years
http://ow.ly/7H1PP
An article on the Pinsent Masons website Out-Law.com (No specific author credit provided).
The article discusses data breaches in the UK where personal data was lost.
The article states, "Figures obtained under freedom of information (FOI) laws showed that 132 local authorities had been involved in personal data loss incidents between 3 August 2008 and 3 August this year, according to a report by Big Brother Watch (BBW)." The article further mentions 1035 data breaches over a 3 year period in the UK alone.
Despite EU regulations requiring protection of personal data, the article states, "The privacy campaigners said that 91% of local authorities had responded to its request for information about the loss of personal data by council employees and contractors during the three year period. It said the information gathered in its report (137-page / 1.95MB PDF) showed that "at least" 35 councils had lost personal data about children and people in care and that information about "at least" 3100 children, young people or students had been "compromised" in 118 cases." A link to the report is provided in the article.
Imagining the Evidence
http://ow.ly/7H0ZU
An article by Craig Ball, Esq. appearing on his blog Ball in Your Court.
This article discusses the use of keywords, and why they often are not as effective as a more advanced approaches can prove to be (when such techniques are properly applied.)
The article states, "Today, it’s commonplace for an opponent to contribute to the list of terms used to search for responsive documents. Unfortunately, experience and study bear out that keyword search is a relatively ineffective means to identify responsive documents, especially when search terms are selected without careful analysis of the collection or testing for precision.
Keyword search is a frustratingly literal technology. If responsive documents contain terms even slightly different from those searched, the responsive documents will likely be missed. Use of stemming, alternate spellings and synonyms helps, but keywords are, at best, a crude tool when you know the collection well and a crap shoot when you don’t."
Mr. Ball believes the future will include discussion of "imagining" the evidence, which will be used in part to help set the parameters used during a predictive coding, or technology enhanced search process.
Sunday, November 27, 2011
Symantec 2011 Information Retention and eDiscovery Survey Global Key Findings
http://ow.ly/7GzVX
A slide share presentation regarding the findings from the Symantec 2011 Information Retention and eDiscovery Survey results.
Some interesting findings are provided throughout the presentation. Of partciular interesting note::
33% of top tier companies are likely to perform litigation hold procedures on back-up systems.
50% are using a formal archiving tool.
36% have prohibition of user self archiving.
Defending the Use of Analytical Software
http://ow.ly/7GfCu
An article by Evan Koblentz posted on law.com on the LTN webpage.
This article discusses the recently completed Advanced eDiscovery Institute Conference held at the Georgetown Law Center. This article provides insight into methods that can be used to defend the use of cutting edge eDiscovery software to enhance the attorney review process, and the associated results of that process.
The article explains, "Judges, opposing counsel, and juries may sometimes ask lawyers about the limitations of concept and keyword searching, the extent to which quality control was performed, and the reasons why results aren't perfect, noted moderator Conor Crowley, of Crowley Law Office in McLean, Va.
Important cases in which the legal basis of software use evolved include Victor Stanley v. Creative Pipe, Disability Rights Council of Greater Washington v. Wash Metropolitan Transit Authority, Gross Construction Association v. American Manufacturers Mutual Insurance, and Datel Holdings v. Microsoft, Crowley said.
One of the best responses is for attorneys to understand and articulate how such technologies work at the process level, the panelists agreed." Links to the referenced case law opinions are provided in the article.
The article further states, "Analytical software can also help clients save money in unexpected ways, such as getting the opposition to pay if they request documents that your software deems unresponsive."
Saturday, November 26, 2011
Southern District of N.Y. Pilot Includes E-Discovery Orders
http://ow.ly/7FZGZ
An article by Mark Michels on law.com on the LTN webpage.
This article discusses a Pilot projected launched to address certain types of litigation in the Southern District of New York, and specifically having certain components that pertain to eDiscovery.
The article states, "At the 2011 Georgetown Law Advanced eDiscovery Institute last week, Judge Shira Scheindlin discussed SDNY Standing Order M10-468, In re: Pilot Project Regarding Case Management Techniques for Complex Civil Cases in the Southern District of New York (Nov. 11, 2011). She explained that the pilot project was the result of a joint bench and bar effort to improve the quality of judicial case management. It will include, among other matters, class actions, multi-district litigation actions, patent, trademark, and securities actions." A link to the Pilot Project information is provided in the article.
The article further outlines some of the components of the Pilot Project, as follows:
- Counsel are "sufficiently knowledgeable in matters relating to their clients" technological systems to discuss competently issues relating to electronic discovery".
- The parties have discussed implementation of a data preservation plan; identification of potentially relevant data; disclosure of the programs and manner in which the data is maintained; identification of computer systems utilized; and identification of the individuals responsible for data preservation, etc.
- The parties have discussed protocols for the search and review of electronically stored information.
- The parties have discussed an FRE 502(d) Order.
12 Gadgets for the Holidays
http://ow.ly/7FI4B
An article on the lawyertechreview.com website written by Geri L. Dreiling, Esq.
This article provides gift suggestions for the holiday season, providing a list of practical gadgets that attorneys would find useful.
The article recommends 12 items, listed below, and provides descriptions of the features and functions of each item:
- Trent iCruiser External Battery Pack
- Belkin Dual-USB Charger
- Apple Wireless Keyboard
- Trent Airbender iPad 2 Case with Wireless Bluetooth Keyboard
- BoxWave Capacitive Stylus for the iPad, iPad 2 and Kindle Fire
- Documents to Go iPad App
- 247 Credit-Card Case for the iPhone 4
- Amazon and iTunes Gift Cards
- Dragon Naturally Speaking
- Amazon Kindle Fire
- Apple iPhone 4S
- Apple iPad 2
Panel Backs Use of GPS Device on State Worker's Personal Car
http://ow.ly/7FGoN
An article in the New York Law Journal by John Caher.
The article discusses use of GPS tracking devices by employers.
The article states, "The state Inspector General's placement of a GPS tracking device on the private vehicle of a government employee suspected of falsifying attendance records did not violate the employee's rights, a deeply divided appeals panel held Wednesday.
The Appellate Division, Third Department, which was previously reversed when it upheld the warrantless use of a GPS device to track a criminal suspect, said the electronic surveillance was justified and reasonable in this civil matter because traditional methods, such as following the employee, had been thwarted."
The article discusses the case, "Cunningham v. New York State Department of Labor, 512036," A link to the case opinion is provided in the article. The case addresses a situation where a former state employee was long suspected of taking unauthorized absences from work and falsifying time records, and the GPS device was used to confirm this
The article further explains, "The inspector general secured a subpoena to obtain Mr. Cunningham's E-ZPass records and also placed a global positioning system device on his personal car at a time when it was parked in a lot near his office.
Over the span of several weeks, the GPS device recorded Mr. Cunningham's movements, allegedly obtaining evidence that he lied about his work hours. Based on that evidence, he was fired." The employee attempted to have the evidence gathered excluded from his disciplinary hearing but the evidence was held to be admissible against him. There was a split in the Justices on this matter, and the Court was seemingly divided over this issue.
Friday, November 25, 2011
Hip Checked – Plaintiffs’ Ediscovery Ploy Rebuffed In New Jersey
http://ow.ly/7Fubw
An article on the drug and device law blog posted by "Bexis".
This article discusses a Federal case involving a mass tort claim, in which a parallel proceeding was taking place in New Jersey State Court.
The article states that certain plaintiff's in the State proceeding objected to the form of eDiscovery production that was agreed to in the Federal proceeding. The plaintiff's objections would have resulted in 7 figures of additional costs to the defendants, and the State court rejected the plaintiff's requests, stating the Federal court form of production was acceptable. The referenced case is In re DePuy ASR™ Hip Implants Litigation, No. BER-L-3971-11, slip op. (N.J. Super. Oct. 18, 2011). A link to the slip opinion is provided in the article.
The article provides quotes from the court's opinion, which cited the Manual for Complex Litigation, and also stated, "It is clear that the MDL Protocol is the result of a "give and take" by and between highly skilled counsel in the MDL and other State court jurisdictions. The MDL Protocol is not the format initially proposed by defense counsel but, as indicated above, presents a reasonable accommodation after negotiations by and between counsel, all of whom were on equal footing. . . . To permit or otherwise Order a format unique to New Jersey would cause an undue hardship on the Defendants."
Use the scalpel first: EDA makes e-discovery a successful operation
http://ow.ly/7F52H
An article by Alon Israely and George Socha appearing on the insidecounsel.com website.
This article discusses the need to utilize the proper technology and tools to create an efficient eDiscovery workflow.
In order to properly proceed with the eDiscovery process, the article states, "The e-discovery team must ask the following questions:
- “Where is the data we need? “
- “How can we separate it from what we don’t want?”
- “How can we find and preserve it easily without inconveniencing a lot of people?”"
The article provides to tips on how to proceed, and offers some idea of various steps that should be followed as part of an overall eDiscovery management plan. The article further states, "The EDA process does not have to be an expensive or cumbersome part of the EDRM process. Rather, it is the entire EDRM process writ smaller, designed with a narrower focus and conducted on a smaller scale. EDA also can become non-burdensome and low-cost when piggy-backed on other e-discovery tasks such as legal hold notification."
Thursday, November 24, 2011
Spilling the Beans on a Dirty Little Secret of Most Trial Lawyers
http://ow.ly/7E47K
This is an article by Ralph Losey, Esq. on his blog e-Discovery Team.
This article discusses the fact that many attorneys still don't understand electronic discovery. The article purports to reveal two secrets, one which is the lack of understanding of eDiscovery, the other of which is not addressed in this article but promises to be revealed in a subsequent writing. The 2nd secret to be revealed has to do with search engine technology.
The article states, "The truth is, the world has changed too fast in the past few decades for most trial lawyers to keep up. As a result, most are incompetent to handle electronic evidence, including discovery of their client’s documents. A majority of trial lawyers are in complete denial of their incompetence. Others admit the painful truth, but just bide their time until retirement. They hope that e-discovery won’t pop up in any of their cases. If and when it does, they see nothing wrong with delegating core lawyer functions to outside vendors. Only a few admit the truth and have the intensity and dedication to do something about it, to put in the hard work to gain personal competence, or, and this is just as good for those who have no aptitude or interest in e-discovery, to bring people into their firm who are competent and then have the wisdom to delegate to them."
The article further states, "See: E-Discovery Competence is a Fundamental Ethical Challenge Now Faced by the Legal Profession, Chapter 34 of my bookElectronic Discovery (West 2010). It is much easier to blame judges or the rules than your friends and colleagues.
Despite this conspiracy of silence, the secret of incompetence is known by all in the trade (although the word incompetent is never used). It is there to be seen by anyone who looks. For instance, a survey of attorneys made by the Federal Judicial Center, Case-Based Civil Rules Survey (2009), found that e-discovery was only discussed in 30% of the 26(f) conferences, which included discussions not to do e-discovery."
In addition, another blog post by Mike McBride, discusses Mr. Losey's article, and provides further insight on this topic. A link to Mr. McBride's article is provided below:
http://ow.ly/7E4fC
P.S. On this Thanksgiving, Mr. Losey offers some wonderful words of thanks in his article, "I am grateful for the freedom I enjoy to speak and write controversial things to try to change the law. I am grateful to live in the U.S.A., a country that not only allows free speech, even if unpopular and anti-establishment, but encourages it, and makes it a core constitutional value. Like all lawyers in the U.S., I have sworn an oath to uphold the Constitution, including especially, for me at least, the First Amendment."
Thanks Giving
http://ow.ly/7E1kP
A blog post on the EDD Update blog by Monica Bay.
This is a blog post offering thanks and good wishes to those in the legal technology community. The writers of the Litigation Support Technology & News Blog also hope that everyone has a great holiday season, and a great 2012 to follow.
As Ms. Bay states, "May this day bring you peace, inspiration, and hope. For those who will spend today with family, speak softly; for those who cannot, be kind to yourself today. Real life does not always play out like a Hallmark card, but there is so very, very much good in this world."
Wednesday, November 23, 2011
Holding powers other branches lack, Congress enters e-discovery fray to probe new rules, growing costs
http://ow.ly/7DE9G
An article by Robert Hilson on the aceds.org (Association of Certified eDiscovery Experts) website.
The article discusses the fact that Congress will become involved in the debate regarding possible revisions to the Federal Rules of Civil Procedure.
The article states, "It will come as a surprise to some who work in e-discovery that Congress is also the ultimate arbiter of the content of the Federal Rules of Civil Procedure, the guidelines by which the 93 US judicial districts handle civil cases. Congress, whose present membership includes 151 lawyers, maintains similar veto power over the rules approved by the Supreme Court that apply in criminal cases."
The article further states, "Led by Congressman Trent Franks, Chairman of the Constitution Subcommittee of the House Judiciary Committee, Congress is about to start receiving evidence of what's going on and why it costs so much.
Since the new rules took effect in 2006, sanctions for mishandling electronically stored information (ESI) have increased greatly. A 2010 study published in the Duke Law Journal found that there were more e-discovery sanctions cases in 2009 than in all prior years since 2005 combined. More recent reports show the trend is continuing. There is wide consensus that e-discovery under the federal rules, and under the distinct rules of some states, is more expensive, more complicated and more contentious than ever." A link to the referenced Duke Law Journal study is provided in the article.
The article further provides some arguments both for, and against, the need to revise the Federal Rules of Civil Procedure. In addition, current subcommittee efforts that are seeking to address some of the "burdens" associated with eDiscovery, and how to potentially reduce the costs associated with preservation obligations are also discussed in this article.
E-Discovery: Does it need to be so expensive?
http://ow.ly/7DDKJ
An article by Daryl Shetterly and Howard Reissner appearing on the insidecounsel.com website.
This article focuses on methods to possibly reduce eDiscovery costs, as well as the Federal Rules of Civil Procedure, and how to comply with those rules while still limiting the expense involved.
The authors state, "In the absence of further guidance from the courts or the Federal Rules, what can an attorney do to reduce both cost and the likelihood of a negative outcome?
There is an aspect of e-discovery expense that in-house and outside counsel are well positioned to influence: Take a closer look at the people, process and technology you use to comply with your e-discovery obligations. There is a big cost difference between an e-discovery project that is properly planned and managed and an e-discovery project that is ad hoc and reactionary.
Many lawyers err on the side of preserving, collecting and reviewing too much information because they are concerned with the small (but potentially very bad for practice building) possibility of missing a few relevant, or worse, privileged documents.
Many lawyers also depend on people who are not well-versed in e-discovery law and technology. They use processes that are not adequate to ensure quality, while minimizing cost and using technology that has fallen behind the evolutionary curve."
The article offers some sound advice, including stating, "Remember that there is no such thing as “e-discovery in a box.” Processes and technology that were only recently best practices are consistently replaced with even better processes that are more defensible and do a better job of integrating technology. Technology continues to evolve and develop in ways that will impact both the types of e-discovery problems we face and the types of solutions we deploy to solve those problems. Software tools adequate a few years ago are now outdated as new tools and data storage become increasingly complex.
As the challenges and complexity of discovery evolve, it is not enough to rely on vendors, software or processes that may have been sufficient several years ago, but are not up to the task of today’s larger and more complex universe of data.
Also, be sure you have the right people managing your technology and process at both the law firm and vendor level. Consider bringing in separate e-discovery counsel to handle the e-discovery aspects of a matter."
Should a Legal Hold “Waiver” Be Secured from Departing Employees?
http://ow.ly/7DCYg
An article by Craig Ball, Esq. on the Ball in Your Court blog.
This article discusses the need to possibly obtain legal "waiver" from employees that are leaving from their position. The article states, "Not every reduction in force is a precursor to litigation; in fact, the majority of terminated employees do not sue their former employers. Yet, any labor lawyer or HR person worth her salt would caution an employer to assess the potential for a subsequent suit and initiate preservation if litigation is reasonably anticipated.
That’s sound advice, but it tends to be overlooked, especially when the separation isn’t marked by angry accusations. Most terminated employees slink off without screaming, “You’ll hear from my lawyer!” How do we bring a soupçon of certainty to the preservation process?"
The article provides a link to another referenced article written by Mark Sidoti, of the Gibbons Law firm. The article referenced by Mr. Ball provides additional insight into this topic.
Legal Issues in the Cloud: Exploring Business Continuity, Liability and SLA-related Issues
http://ow.ly/7CNB0
An article by Andrew L. Goldstein appearing on the Computer Technology Review website.
This article is the 2nd part of a series that discusses legal issues related to the use of cloud computing. The author discusses legal liability, service level agreements and the control of corporate data that is held by a cloud computing provider.
The article states, "Many companies are familiar with ‘e-discovery’ and have data retention, storage and destruction policies in place that apply in the event of litigation. If a cloud customer is sued, or there is the threat of litigation, the customer may have to initiate a ‘litigation hold’ to preserve documents, including electronic documents and any metadata in the documents. This could present a challenge in the cloud if the customer’s data is commingled with that of other clients or if the customer’s data is stored on parallel servers. Cloud customers should determine the vendor’s ability to prevent the destruction, alteration or mutilation of customer data in the vendor’s possession, as well as the vendor’s search capabilities for the data. Cloud customers should also make sure that their corporate policies and procedures account for any data in the cloud. Do the data retention and destruction policies of the cloud vendor align with those of the customer?"
The article further states, "Many cloud vendors subcontract with other entities. For example, in the SaaS environment, a third party often hosts the software vendor’s programs. The issues discussed above are complicated by the cloud vendor’s use of subcontractors. Will the subcontractor allow access to the customer’s data? Can the subcontractor comply with a litigation hold? For jurisdictional issues, where is the subcontractor located?
If there is a dispute between the customer and the cloud vendor, the vendor may try to shift liability to the subcontractor and the customer may not have the right to bring an action directly against the subcontractor. Some customers try entering into direct contractual relationships with the subcontractor. For instance, in the SaaS scenario, the customer might enter into an agreement with the SaaS vendor and also with the hosting service used by the SaaS vendor."
Lists, Forums, Social Media, and Thanksgiving
http://ow.ly/7CKFB
An article by Evan Koblentz posted on law.com on the LTN webpage.
This article discusses resources that are available for those that are interested in content about the topic of legal technology.
The article references several sites and forums that can be used to read content about legal technology, or engage in dialogue about this topic.
The article states, "Whichever approach you prefer -- free and open, paid and closed, or even a social approach like the various LinkedIn groups (such as the Legal IT Network and Law Technology News' own group) -- the bottom line is that legal technology users can help each other to decrease hype and increase productivity." A link to the referenced groups is also provided in the article.
Tuesday, November 22, 2011
A Growing Trend: Use of E-Discovery 'Special Masters'
http://ow.ly/7CfRu
An article by Monica Bay appearing on law.com on the LTN webpage.
This article touches on discussions that took place at the recently completed Georgetown Advanced eDiscovery Institute conference regarding the use of Special Masters to assist with eDiscovery disputes, and pilot programs designed to further this trend.
The article quotes eDiscovery and forensic expert Craig Ball, Esq., "Craig Ball, who writes LTN's e-discovery column, "Ball in Your Court," frequently serves as an EDD special master, and summed up the typical job description in a May 2009 LTN article, "Special Masters."
"It's an amalgam of judge and expert and Oprah, with a lot of computer geek," explained Ball. "Sometimes, I'm standing in the judge's shoes kicking rumps to get a derailed, contentious e-discovery effort back ontrack. Other times, I'm the court's neutral insuring that responsive ESI is produced and privileged information is protected. Or, I'm the computer forensic examiner tasked with determining if a litigant destroyed electronic evidence and if it can be recovered," he notes." A link to the referenced article by Craig Ball is provided in Ms. Bay's article.
The article further states, ""An EDD special master adept at understanding the feasibility, complexity, impact and cost of identifying, processing, producing and using the panoply of data encountered in modern life (from the contents of a thumb drive to large enterprise information systems and cloud providers) can help everyone move forward in a sensible, cost-effective and (at times) creative fashion," explained Ball, a longtime member of LTN's Editorial Advisory Board and the LegalTech advisory board."
E-Discovery: Waging a strong e-discovery offense
http://ow.ly/7BE46
An article on the insidecounsel.com website written by Matthew Prewitt.
This article discusses the role of an eDiscovery consultant, and specifically addresses tactics related to an "offensive" strategy, as opposed to a responsive role.
The article states, "First, waging an aggressive e-discovery offense requires having confidence that your company’s own e-discovery is defensible."
The article wisely advises, "Because of the frequent high-stakes battles over e-discovery sanctions, too many attorneys equate an aggressive e-discovery strategy with posturing the case for a potentially dispositive sanctions motion. In most cases, however, your company’s primary e-discovery objective should be the tried and true strategy of obtaining evidence in your adversary’s possession that will help win your case. Counsel who are angling for an e-discovery sanctions battle may miss valuable opportunities to win the case the old-fashioned way: proving the merits of the client’s claims and defenses."
The author further mentions, "By maintaining a friendly and constructive demeanor, your trial counsel and retained consultant may readily induce opposing counsel to rely on their technical advice and insights when negotiating the parameters of your adversary’s preservation, search and production protocols."
The article also addresses situations to be wary of, and discusses scenarios where the opposing side might be looking to gain advantages by not properly handling their eDiscovery obligations. The article states, "In short, I share the view expressed by many that there are too many sanctions motions arising from e-discovery and the awarding of significant and potentially dispositive sanctions for e-discovery violations is encouraging unnecessary and distracting motion practice. In most cases, going on the e-discovery offensive should mean only that your counsel and consultant are asking hard questions in discovery conferences with your company’s adversary and demanding a reasonably complete production.
However, there are still some cases where it is essential to seek relief from the court."
eDiscovery Trends: Potential ESI Sources Abound in Penn State Case
http://ow.ly/7Bz1v
An article by Doug Austin on his blog eDiscovery Daily.
This article discusses the investigation into the charges surrounding the Penn State scandal.
The blog post states, "Seth Row, an attorney with Parsons Farnell & Grein LLP in Portland (OR), has written an article published in the Association of Certified eDiscovery Specialists (ACEDS) web site providing a detailing of potential sources of ESI that may be relevant in the case. The article illustrates the wide variety of sources that might be responsive to the litigation. Here are some of the sources cited by Row:
- Videotape of entry and exit from the athletic facilities at Penn State, to which Paterno gave Sandusky access after the latter resigned in 1999;
- Entry/exit logs, which are likely housed in a database if keycards were used, for the Lasch Football Building, where abuse was allegedly witnessed
- Phone records of incoming and outgoing calls;
- Electronic rosters of football players, coaches, staff, student interns, and volunteers affiliated with the Penn State football program over time;
- The personal records of these individuals, including telephone logs, internet search histories, email accounts, medical and financial records, and related information created over time;
- University listservs;
- Internet forums – a New York Times article reported last week that a critical break in the investigation came via a posting on the Internet, mentioning that a Penn State football coach might have seen something ugly, but kept silent;
- Maintenance logs maintained by the two custodial employees who allegedly witnessed abuse;
- Identities of all media beat reporters who covered the Penn State football team;
- Passenger and crew manifests for all chartered flights of the Penn State football team in which Sandusky was a passenger;
- Sandusky's credit card records to document meals and outings where he may have been accompanied by victims, and records of gifts he purchased for them;
- All records of the Second Mile Foundation identifying boys who participated in its programs, as well as the names of donors and officers, directors and staff;
- Paper record equivalents of this ESI that were produced in the 1990s before electronic recordkeeping became prevalent;
- All electronic storage and computing devices owned or maintained by Sandusky, Paterno and other central figures in the scandal, including cell phones, personal computers, tablet computers, flash drives, and related hardware."
A link to Mr. Row's article is provided in the blog post, an additional link to the referenced NY Times article is also provided.
'Thought Leadership' in the World of Social Media
http://ow.ly/7BxyP
An article by Adrian Dayton published by the National Law Journal, and appearing on law.com on the LTN webpage.
This article provides insight from an interview Mr. Dayton conducted of James Durham, a lawyer and chief marketing officer of McGuireWoods.
The article describes Mr. Durham's input as to how to help young attorneys focus on becoming thought leaders. He advises them to write three columns on a page, the first is to list active clients and work, the 2nd is to list work that can be done for those clients, and the third column is to list interests that the attorney enjoys. The article states, "Durham used these three columns to help even the young lawyers understand that they are already developing thought leadership--and that asking the right questions can help them focus their efforts."
The article further states that social media has made it easier for attorneys to get their names out there.
Document Preservation: Spoliation and the "Ultimate Sanction"
An article posted on the eDiscovery Law Review website of Cozen O'Connor by Diana Lin.
This article focuses on recent case law developments, particularly two new cases, regarding document preservation obligations.
The article focuses on the cases of Gentex Corp. v. Sutter, No. 3:07-CV-1269, 2011 U.S. Dist. LEXIS 122831 (M.D. Pa. Oct. 24, 2011), and Cedar Rapids Lodge & Suites, LLC v. JFS Dev., Inc., No. C09-0175, 2011 U.S. Dist. LEXIS 110671 (N.D. Iowa Sept. 27, 2011). In both of these matters, sanctions were sought for improper conduct during discovery, as potential evidence was destroyed. The Gentex case granted default judgement, but in the Cedar Rapids case the court refused to go that far.
The article states, "The court ultimately determined that granting default judgment to Gentex was the “least onerous” sanction corresponding to the willfulness of the spoliation, given Sutter and Walko’s “unabashedly intentional destruction of relevant, irretrievable evidence.”"
With respect to the other matter, the article states, "...the district court determined that there was no proof that the defendant intentionally engaged in spoliation. As an initial matter, the court seemed impressed by the sheer volume of documents that plaintiffs had already recovered from the defendants. The defendant had initially produced 875 documents followed by an additional 2,700 pages, not to mention the 34,000 documents extracted from various hard drives and computers.
Additionally, the court found that plaintiffs had not met the relevant legal standard. To warrant any sanction, much less a default judgment, the court had to find: 1) intentional destruction indicative of a desire to suppress the truth; and 2) actual prejudice to the other party resulting from the spoliation."
Additionally, the court found that plaintiffs had not met the relevant legal standard. To warrant any sanction, much less a default judgment, the court had to find: 1) intentional destruction indicative of a desire to suppress the truth; and 2) actual prejudice to the other party resulting from the spoliation."
Monday, November 21, 2011
Pounding The Gavel On E-Discovery
http://ow.ly/7B2iq
An article by Sheri Qualters posted on law.com on the corporate counsel website.
This article discusses the recently proposed model rule for eDiscovery in patent litigation.
The article states, "...Chief Judge Randall Rader unveiled a model order designed to limit discovery in patent cases.
Rader announced it himself at the Eastern District of Texas Bench Bar Conference, where he told a standing-room-only crowd that the Federal Circuit Advisory Council had unanimously voted to adopt his proposal. They are voluntary guidelines that may be used by any district court or judge.
The order proposes several limits on the production of electronically stored information. Prominent among them:
- Metadata is excluded from e-discovery production requests without "a showing of good cause."
- Courts may consider up to five additional custodians per producing party and five additional search terms per custodian. Litigants who submit e-discovery requests that exceed court orders and the parties' agreement must pay for the extra production.
- Receiving parties are barred from using e-discovery that the producing party asserts is attorney-client privileged or work product–protected.
- The mass production of electronic information, or the inadvertent release of privileged or work product data, is not a waiver or permission to use it."
The article further states that the purpose of this proposed order is to limit the cost and burden associated with eDiscovery.
P.S. What are your thoughts on this proposed Model Order? Will it gain acceptance? Does it really help solve any of the challenges associated with the costs of preserving and producing ESI? Will it provide an improvement in reaching "just and fair" results.
Georgetown Panel Focuses on Discovery Rules
http://ow.ly/7B1BY
An article by Evan Koblentz on law.com on the LTN webpage.
This article discusses the recently concluded Georgetown Advanced eDiscovery Institute conference.
The article states, "A wide-ranging discussion about e-discovery and the Federal Rules of Civil Procedure highlighted Friday morning's sessions at the Georgetown Law Center Advanced eDiscovery Institute.
The panel, "Future of the Rules/New Developments," included federal judges Joy Flowers Conti, of Pittsburgh, Paul Grimm, of Baltimore, and Lee Rosenthal, of Houston, along with attorneys William Butterfield of the Hausfeld law firm and Jeane Thomas of Crowell & Moring, both of Washington, D.C."
The article further states that Ms. Thomas stated, "17.5 GB per custodian, averages four custodians per matter, has 329 matters on hold (a third of them are active cases), and collects more than 700 MB for every 2.3 MB that are actually used. Those kinds of figures, along with controversial cases such as Pippins v. KPMG, can put fear in the hearts of large companies, she said. However, she doesn't "favor a very, very detailed rule," because techology moves too fast for such a rule to keep up."
E-Discovery Times Are a Changin’…Or Are They?
http://ow.ly/7AIMN
An article by Devin Krugly From the website eDiscovery Insight.
This article provides some commentary in response to the findings set forth by the Fulbright annual litigation trends report.
The article states, "...The Federal Rules Advisory Committee (“Advisory Committee”) met just last week in Washington, D.C., primarily to discuss a sanctions-based approach to enforce certain preservation practices within e-discovery. Depending on how such a rule is crafted it could force parties with e-discovery obligations to take preservation even more seriously than many do today. It’s hard to imagine a more extreme approach than “collect everything and sort it out later”, but some may expand current practices to avoid sanctions resulting from negligence or bad faith. In my opinion it is hard to see stricter penalties resulting in more cooperation – and they would more likely portend additional time, effort and ultimately expense associated with e-discovery."
In addition, the article references that 18% of respondents mention having to collect social media from an employee's personal account. The article mentions, "It seems to me that this 18% is probably just the tip of a looming iceberg and even if companies get wiser about limiting social media access at work, the need to collect from this medium is just going to increase. Better start swimming or you’ll sink like a stone, so to speak."
The South's Richest General Counsel: GC Salaries Stagnate in 2010
http://ow.ly/7AHDr
An article by Katheryn Hayes Tucker posted on law.com on the corporate counsel webpage.
This article discusses salary trends for general counsel.
The article states, "Of the top 10 highest-paid GCs in public companies across the Southeast, the average 2010 compensation package totals roughly $4.9 million—from $9.2 million at the top to $3.7 in the 10 spot. That's slightly up from $4.3 for 2009. But neither of those years was as good for the top 10 as 2008, when the average was $5.5 million, or 2007, when it was $5.6 million. Still, no drastic changes in those four years.
Raj M. Nichani, president of RMN Global Search, said he doesn't think overall compensation for CLOs has moved " dramatically up or dramatically down. It's pretty stagnant," Nichani said. "But what's happening is their hours have gone up. Usually, that's a pretty sure pay raise. But they don't get that kind of love in this legal market."" A link to the to 10 highest paid in the Southeast is provided in the article.
Raj M. Nichani, president of RMN Global Search, said he doesn't think overall compensation for CLOs has moved " dramatically up or dramatically down. It's pretty stagnant," Nichani said. "But what's happening is their hours have gone up. Usually, that's a pretty sure pay raise. But they don't get that kind of love in this legal market."" A link to the to 10 highest paid in the Southeast is provided in the article.
Legal spend: The right metrics with the right technology platform
http://ow.ly/7AfLw
An article by Keith Okano on the legalitprofessionals.com website.
This article touches on the need to provide metrics for a corporate law department, so they can properly utilize technology to enhance the performance of their in-house law department, and reduce their legal expenditure.
The article states, "Technology and the metrics it provides are literally changing the way savvy law departments do business. It’s no longer enough to reduce overhead or outside counsel spend, now is the time to improve legal services both internally and externally, lower the overall cost of these services, and become strategic partners of business units."
The article further states, "Metrics gleaned from dashboards and established key performance indicators (KPIs) are enabling legal staff to go beyond merely tracking both outside and inside spend. These metrics also provide the transparency necessary to demonstrate the value of the legal service being delivered by enabling legal departments to:
- provide the insight needed to drill down and make critical decisions such as what matters can be in-sourced rather than outsourced – and in the case of outsourcing, if a firm’s offer to take on certain litigation is beneficial in terms of cost and performance
- identify risk and various cost drivers and address those issues in real time
- identify key trends such as specific types of litigation and related performance
- identify when it is beneficial to spend more to protect intellectual assets
- accurately predict annual spending
- provide specific data for compliance reporting, 10K reporting, financial planning."
Ruminations on the Ethics of Law Firm Information Security
http://ow.ly/7AeRC
An article on the website SLAW written by Sharon D. Nelson and John W. Simek.
This article focuses on requirements imposed on law firms to keep client data secure and confidential.
The article discusses ABA rules, and focuses on Model Rule 1.6, quoting the terms set forth by this rule. The article then states, "Are lawyers abiding by their ethical duty to preserve client confidences? Our opinion is that they are not. Here are a few reasons why we have that opinion:
- Security expert Rob Lee, a noted lecturer from the security firm Mandiant has reported to us that Mandiant spent approximately 10% of its time in 2010 investigating data breaches at law firms.
- Security expert Matt Kesner, who is in charge of information security at a major law firm, reports that his firm has been breached twice – and that he is aware that other law firms have suffered security breaches – and failed to report them to clients.
- Our own company, Sensei Enterprises, Inc., has never performed a security assessment at a law firm (or for that matter, at any kind of business) without finding severe vulnerabilities that needed to be addressed.
P.S. As law firms continue attempting to handle issues pertaining to client data in-house, such as processing of ESI for eDiscovery, this issue of client confidentiality will continue to be one to closely watch.
Full disk encryption is too good, says US intelligence agency
http://ow.ly/7AdWt
An article by Sebastian Anthony on the extreme tech website.
This article discusses full encryption of hard drives, and itemizes some of the concerns that this technology causes for law enforcement, and national security.
The article states, "...there are three main problems with full disk encryption (FDE): First, evidence-gathering goons can turn off a computer (for transportation) without realizing it’s encrypted, and thus can’t get back at the data (unless the arrestee gives up his password, which he doesn’t have to do); second, if the analysis team doesn’t know that the disk is encrypted, it can waste hours trying to read something that’s ultimately unreadable; and finally, in the case of hardware-level disk encryption, tampering with the device can trigger self-destruction of the data."
The article references a recent paper entitled, "The growing impact of full disk encryption on digital forensics,” and provides some commentary regarding that work. The referenced paper provides some tips into how to alleviate some of the concerns mentioned in the Mr. Anthony's article. Although the article points out that more research is needed on this topic as the existing technology does not seem to overcome the challenges associated with recovering data from an encrypted drive.
Subscribe to:
Comments (Atom)